Interlock Ransomware Threat Landscape: Insights from the 2025 Kettering Health Attack
By Rodrigo Luna
In 2025, Interlock has rapidly evolved into a high impact ransomware operator leveraging social engineering lures, multi stage payload delivery, and data leak extortion to pressure victims. Security research highlights their use of techniques such as “ClickFix” style deceptive prompts, compromised websites, and stealer tool deployments during initial access phases. (Sekoia, 2025)
The attack on Kettering Health serves as the year’s defining example, with the group claiming theft of 941 GB of sensitive data and healthcare operations reporting significant service disruptions following the incident (Dayton Daily News,2025)
About Interlock
Interlock conducts coordinated multi stage ransomware campaigns that rely on social engineering for initial access, followed by credential harvesting, data theft, and high impact encryption across a range of operating systems. Public reporting consistently shows the group prioritizing double extortion, stealing large volumes of sensitive data before deploying ransomware to increase pressure on victims. Interlock has been observed targeting organizations in the healthcare and public services sectors. Reported victims include DaVita, Texas Tech University Health Science Center, Drug and Alcohol Treatment Services, Brockton Neighborhood Health Center, and Naper Grove Vision Care, along with their most significant attack of 2025 involving Kettering Health.
Kettering Health Attack Details
Kettering Health is a non-profit healthcare system in western Ohio that operates a large network of hospitals, specialty centers, and outpatient clinics. It includes roughly 14 medical centers and more than 120 care locations, supported by a workforce of thousands of physicians and staff. In May 2025, the organization suffered a ransomware attack in which the Interlock group gained unauthorized access from April 9 to May 20 and accessed or copied sensitive patient data. The attack caused a system wide outage, disrupted operations, and led to the leak of approximately 941 GB of stolen data. Core systems, including Epic and MyChart, were restored in early June, and security enhancements were implemented. The breach was reported to HHS with a placeholder of 501 affected individuals, though the final total is still pending. (HIPAA Journal, 2025)
The following timeline was compiled by The HIPAA Journal:
- Apr 9, 2025: Interlock gains unauthorized access to Kettering Health’s network.
- May 20, 2025: Attack is detected; system-wide outage forces staff to revert to manual processes.
- May 21–30, 2025: Public updates issued; warnings released about scam calls, texts, and emails.
- Jun 2–3, 2025: Core Epic EHR functionality is restored; emergency departments return to normal operations.
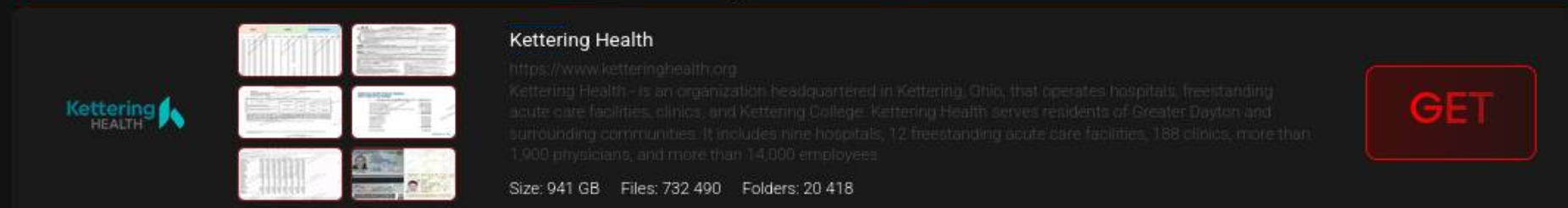
- Jun 5, 2025: Interlock leaks approximately 941 GB of stolen data on its dark web site. (Figure 2)
- Jun 9–10, 2025: Surgeries, imaging, pharmacy services, physician visits, and full MyChart access resume.
- Jun 13, 2025: Normal operations for key services confirmed.
- Jul 21, 2025: Breach reported to HHS with a placeholder count of 501 individuals.
- Oct 17, 2025: Review confirms extensive patient information was compromised.
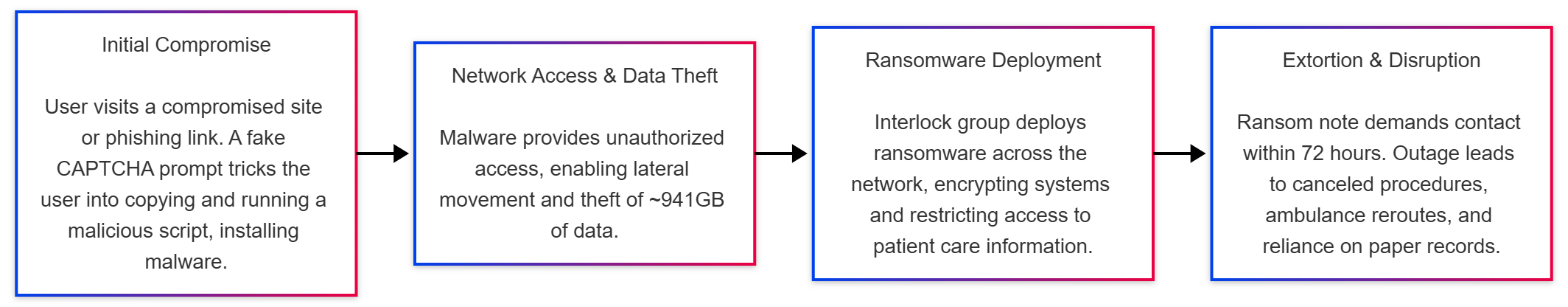
Figure 1 below provides a visual summary of the attack sequence, from the initial compromise through data theft, ransomware deployment, and operational disruption.
Operational Model
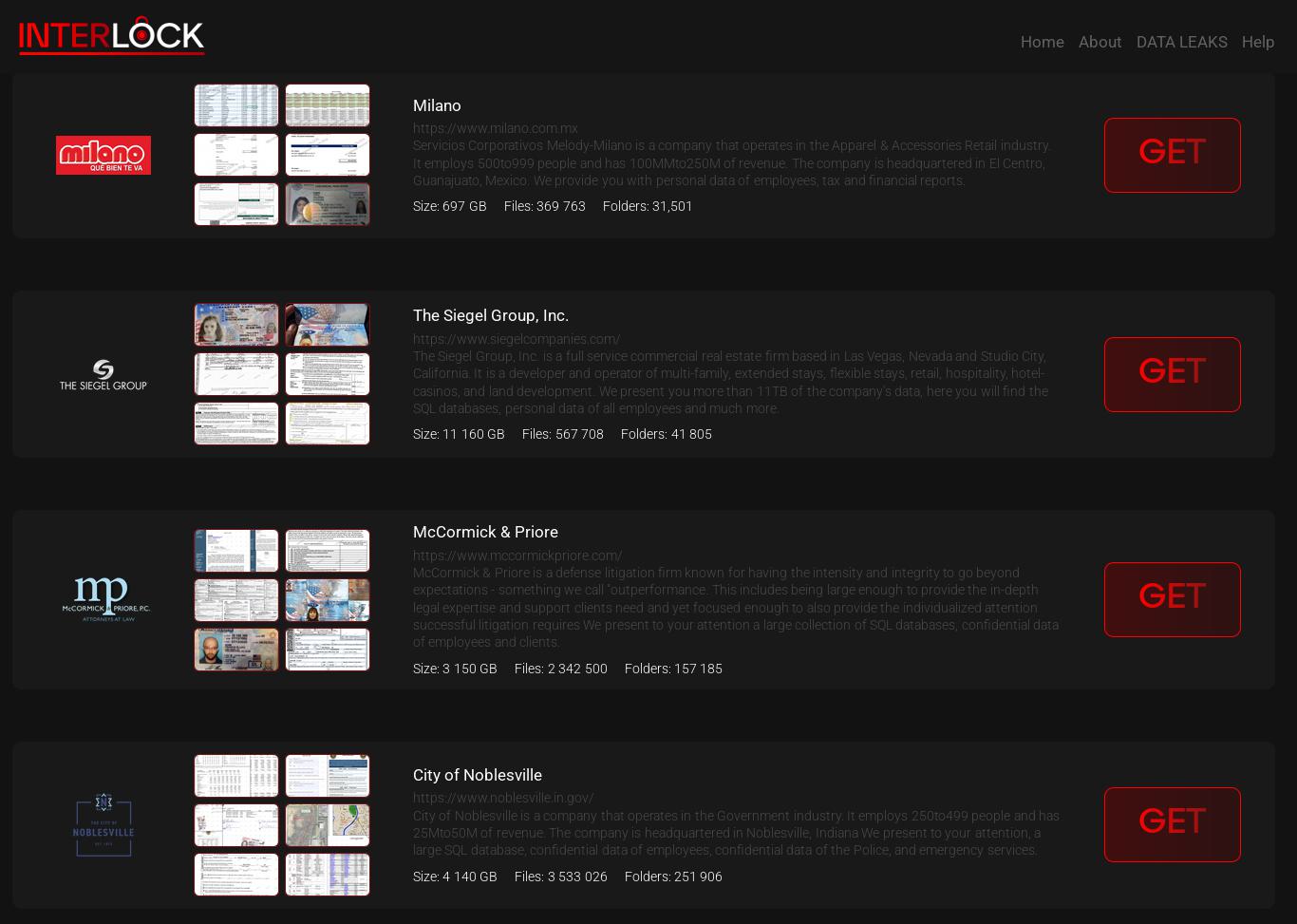
Interlock operates as a privately run ransomware group, not a traditional RaaS program. Research indicates no public affiliate recruitment, and campaigns appear to be conducted by a single, centralized operator rather than a large affiliate ecosystem. The group also maintains a private leak site known as the “Worldwide Secrets Blog”, which is used to publish sensitive data stolen from victims who refuse to pay. The site functions as the group’s public pressure mechanism, listing victim organizations, displaying breach announcements, and hosting links to leaked files. (Figure 2)

The group’s operations are further characterized by:
- Financial motivation, with extortion as the primary objective.
- Double extortion tactics, stealing sensitive data before encryption to strengthen leverage.
- Social engineering based initial access, often via fake update prompts or malicious redirects.
- Credential harvesting using stealer malware or lightweight backdoors to expand access.
- Lateral movement through legitimate remote services and compromised accounts.
- Data staging and exfiltration prior to deploying ransomware payloads.
- Multi platform ransomware deployment, enabling impact across Windows, Linux, BSD, and ESXi.
- Leak site extortion, where stolen data is published to pressure victims into paying.
Delivery and Attack Chain
Interlock relies on delivery methods that mimic normal software activity, according to Arctic Wolf (ArticWolf, 2025). The group often compromises legitimate websites and turns them into fake update pages that prompt users to run commands or installers that appear routine. This approach blends into expected browser behavior and helps the intrusion bypass traditional endpoint defenses. Interlock has also been observed using the ClickFix social engineering technique, a method that presents users with false security or update prompts and guides them to run a copied PowerShell command. This tactic exploits user trust in familiar system messages and provides a reliable path for delivering the initial payload. (Centripetal, 2025)
Initial Access
- Users are redirected to a fake browser update or ClickFix page hosted on a compromised site.
- Victims are instructed to run an installer or paste a command, believing they are correcting an issue or updating their browser.
- A legitimate Chrome or Edge installer may run as a decoy while a malicious PowerShell script executes silently in the background.
- The script becomes the initial foothold, gathering basic system information and opening communication with attacker infrastructure.
Execution and Stealth
- The PowerShell backdoor runs without a visible window and relaunches itself to remain hidden from the user.
- It regularly contacts remote servers for new instructions or payloads.
- Obfuscated commands and encoded strings are used to avoid simple signature-based detection.
- At this stage, Interlock operators may deploy tools such as Interlock RAT or NodeSnake RAT for command execution and remote control.
Persistence and Tooling
- Some script versions add persistence through registry changes to ensure the backdoor remains active after reboot.
- The attackers may download a credential stealer or keylogger through PowerShell to collect credentials for lateral movement.
- Tools such as Azure Storage Explorer and AzCopy have been reported for accessing and uploading data to cloud storage.
- Data exfiltration can also involve WinSCP or similar file transfer utilities.
Infrastructure and Evasion
- Early communication often passes through TryCloudflare tunnels, using temporary subdomains that resemble normal Cloudflare use.
- This helps blend command and control traffic into legitimate patterns and makes it harder to block the attacker’s infrastructure.
Interlock Operational Ecosystem
The group operates within a broader ecosystem that supports its delivery methods and post compromise activity (Sekoia, 2025). The following tables provide a condensed overview of the tooling and techniques observed across Interlock operations:
Tools
| Category | Tools | Purpose | TTP |
|---|---|---|---|
| Stealers | LummaC2, BerserkStealer | Credential theft and browser data harvesting | Credential access, session theft, reconnaissance |
| Malicious Scripts | Obfuscated PowerShell commands | Payload retrieval and execution | Command execution, defense evasion, script-based delivery |
Campaign Techniques
| Technique | Description | TTP |
|---|---|---|
| ClickFix / Fake Updates | Fake update or fix prompts that trick users into running PowerShell commands | Social engineering, user execution, initial access |
| ClearFake-style Redirects | Redirect chains leading to fake update or alert pages | Drive-by compromise, malicious redirection |
| Fake Browser Alerts | Deceptive browser messages or reCAPTCHA-style prompts | Social engineering, user execution |
| Copy, Paste Execution Flow | Victims copy and run malicious PowerShell commands | Command execution through user interaction |
| Obfuscated Script Delivery | Encoded and obfuscated commands used to evade detection | Defense evasion, obfuscated files/scripts |
| Rotating Malicious Domains | Use of many short-lived domains tied to the ecosystem | Infrastructure rotation, domain fluxing |
Centripetal’s Perspective
As Interlock continues conducting ransomware operations across multiple sectors, Centripetal is performing focused analysis on external indicators associated with the group to better understand its infrastructure, delivery methods, and operational patterns. By compiling known indicators linked to Interlock, we can identify the consistent behaviors that define the group’s external operations and campaign activity. This intelligence driven approach provides a clearer picture of how Interlock operates and supports ongoing efforts to track changes in its tactics and external footprint.
Centripetal’s internal analysis of indicators associated with the Interlock ransomware group aligns closely with findings published by several leading security firms. The distribution of observed activity across business sectors within our customer base mirrors what has been documented in external reporting, reinforcing the accuracy of our assessment and confirming that Interlock’s targeting patterns remain consistent across independent intelligence sources.
A notable example comes from Hunter Strategy’s 2025 (Hunter Strategy, 2025) threat assessment on Interlock, which reports results consistent with our own analysis. As shown in Figure 3, more than 59 percent of events matching indicators associated with known Interlock activity were observed within the healthcare sector across Centripetal’s customer base. Hunter Strategy’s insights (Figure 4) reflect the same trend, further validating the accuracy of our attribution and the reliability of the indicators identified within Centripetal’s datasets.
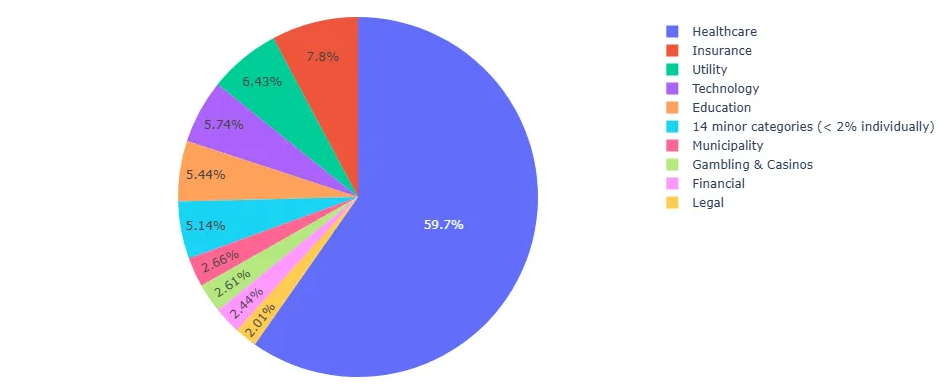
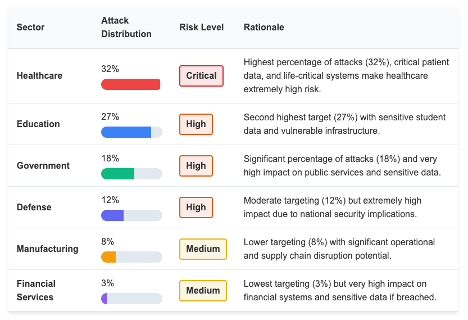
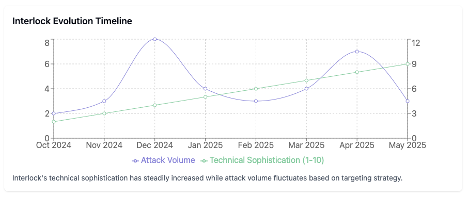
The consistency of these findings is further supported when comparing them with the attack timeline shown in Figure 5. Since December 2024, eight healthcare related attacks have been registered and attributed to Interlock, making healthcare the top targeted sector. This observation reinforces Centripetal’s own results, which show that healthcare organizations consistently generate the highest volume of matched indicators and attempted activity linked to Interlock’s infrastructure across our customer environments.
When viewed alongside sector distribution data and external assessments, the updated timeline provides additional confirmation. Interlock’s operational tempo and targeting preferences remain steady, with healthcare serving as its primary point of impact. The alignment between our internal telemetry, Hunter Strategy’s analysis, and publicly documented attack sequences reflects a coherent pattern of behavior that underscores the group’s sustained and deliberate campaign strategy. Interlock continues to prioritize high value environments where operational disruption has immediate and severe consequences.

To contrast these findings with the previous attack timeline, we analyzed indicators in Centripetal’s threat intelligence month by month to align with periods where Interlock demonstrated the highest activity. During April 2025, nine attacks were recorded according to the referenced analysis. To illustrate the pace at which indicators are identified, incorporated, and deployed within Centripetal’s threat intelligence and across our customer environments, the graphs in Figure 6 show the progression of coverage for these indicators of compromise as attacks unfolded throughout the second quarter of 2025.
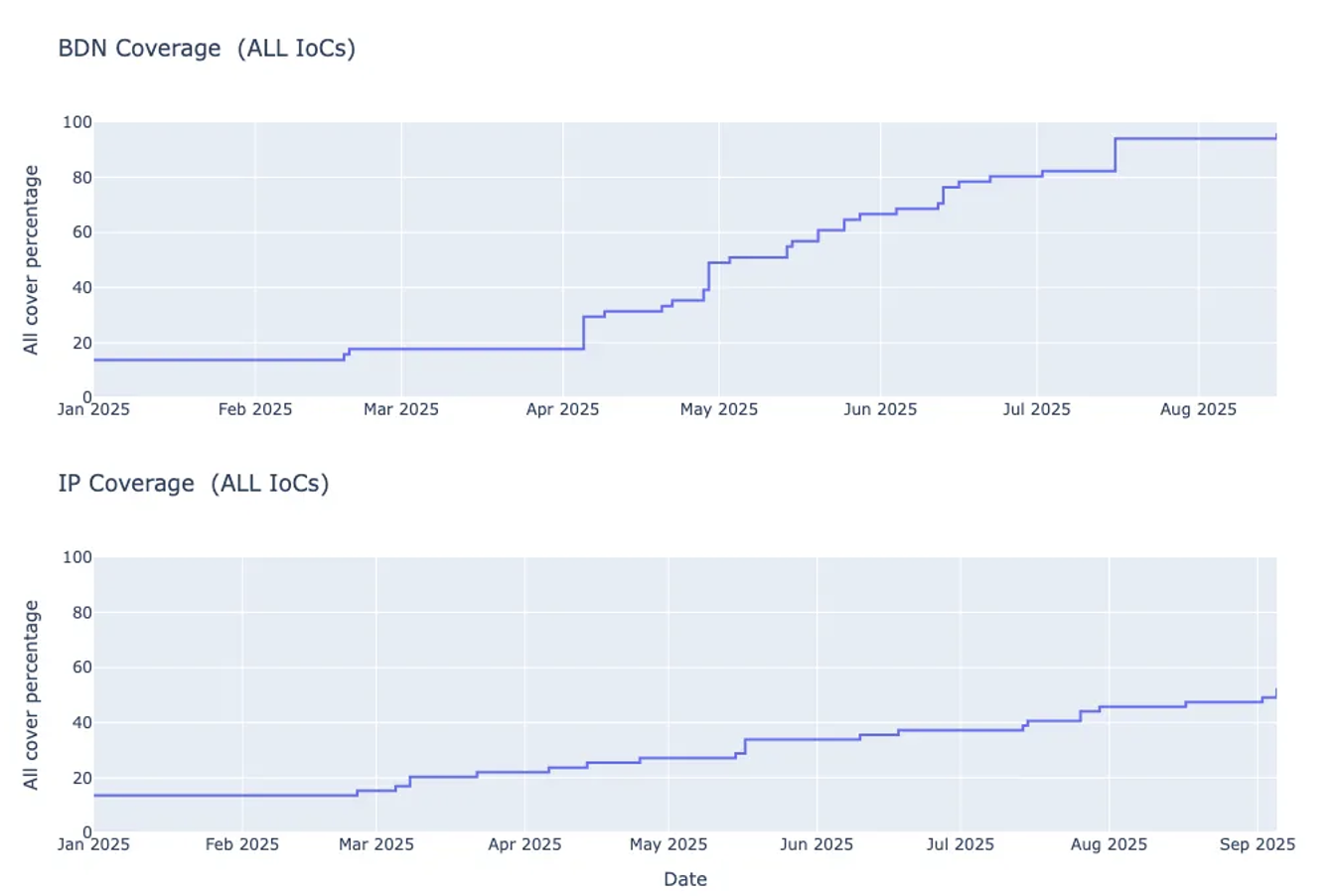
Because ransomware indicators require verification and are often sourced from ongoing or undisclosed investigations, they are rarely available immediately after an attack. This delay means that the progression of coverage in the previous graphs reflects both the discovery of new indicators and the gradual release of validated intelligence over time.
The spike in attack volume between February and April shown in Hunter Strategy’s timeline (Figure 7) also aligns with the rapid increase in IOC coverage observed within Centripetal’s datasets during the same period. As Interlock intensified its operational activity, a corresponding surge of validated indicators entered our threat intelligence pipeline, resulting in the noticeable rise in coverage depicted in Figure 6. This correlation demonstrates that Centripetal’s IOC expansion closely tracks real world attack tempo, with peaks in adversary activity directly reflected in the pace at which indicators are identified, enriched, and deployed across our defenses.
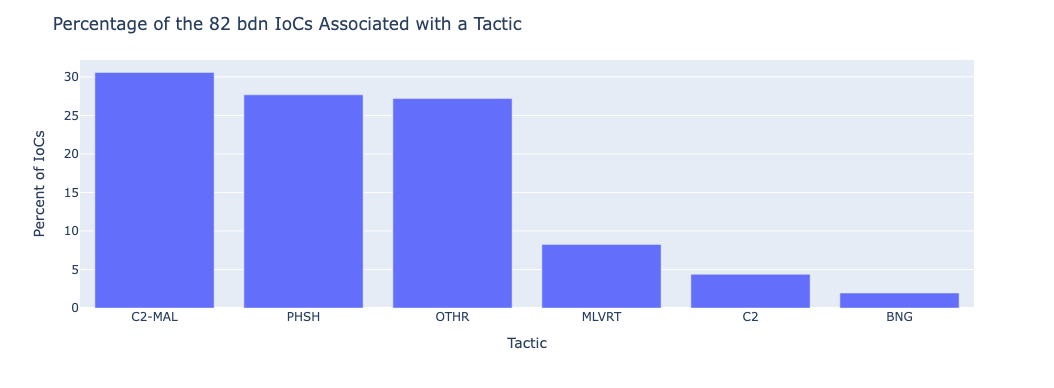
Another strong indicator of Interlock’s operational model is the distribution of IOCs by tactic. Centripetal’s threat intelligence not only identifies malicious infrastructure but also classifies indicators based on the role they play within the attack chain. As shown in Figure 8, analysis of 82 domains attributed to Interlock reveals that over half support malware delivery, command and control activity, or phishing operations. These categories align closely with Interlock’s known reliance on staged payload servers, short lived C2 infrastructure, and email based initial access. The remaining domains function as redirectors or auxiliary infrastructure that supports execution and lateral movement. This distribution reinforces broader industry reporting on Interlock’s tactics and validates the accuracy of Centripetal’s indicator attribution.
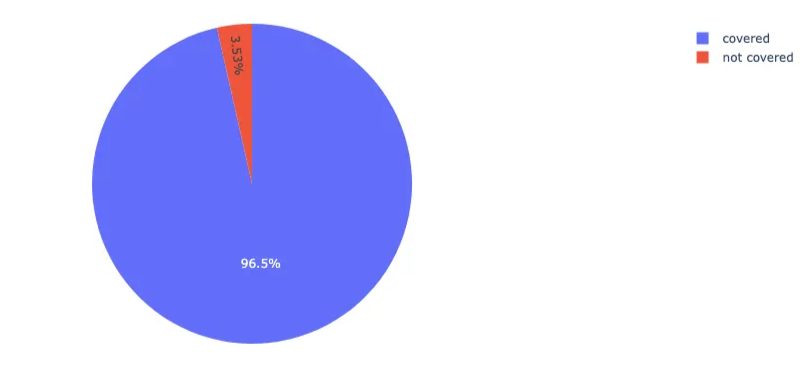
Coverage analysis of 85 Interlock attributed domains further validates the strength of Centripetal’s threat intelligence, with 96.5% already incorporated into our detection and shielding capabilities at the time of evaluation. This high level of coverage demonstrates the effectiveness of our intelligence ingestion pipeline and its ability to rapidly absorb and deploy indicators associated with active ransomware campaigns. The small portion of domains not yet covered reflects the typical delay between the moment an IOC first appears in the wild and when it becomes publicly documented or validated by Intelligence sources. Overall, the results reinforce that Centripetal is proactively shielding customers from the vast majority of Interlock’s known malicious infrastructure.
Overall, the alignment between Centripetal’s telemetry, external reporting, and IOC coverage shows that Interlock remains a focused and consistent ransomware threat, with healthcare continuing to be its primary target. The group’s reliance on social engineering, staged payload delivery, and short lived infrastructure is reflected across both internal and third party datasets, reinforcing confidence in the indicators attributed to its operations. Centripetal’s rapid integration of validated IOCs ensures strong visibility into Interlock’s activity and supports proactive protection for customer environments as the group’s campaigns continue to evolve.
Centripetal is also pleased to offer Penetration Testing and Vulnerability Assessment services to help organizations identify vulnerabilities and reduce risk. If interested, please contact our Professional Services team at profservs@centripetal.ai or reach out to your Centripetal Account Representative.
Resources
- The HIPAA Journal - Kettering Health Confirmed Patient Data Compromised in May 2025 Ransomware Attack
- Kettering Health - Cybersecurity Incident
- Dayton Daily News- Ransomware group claims it stole more than 730,000 files from Kettering Health
- Security Week - Ransomware Gang Leaks Alleged Kettering Health Data
- Industrial Cyber - Ransomware suspected in Kettering Health cyberattack disrupting patient services, canceling elective procedures
- CISA - #StopRansomware: Interlock
- Arctic Wolf - Threat Actor Profile: Interlock Ransomware
- Picus Security - Interlock Ransomware Analysis, Simulation, and Mitigation - CISA Alert AA25-203A
- Sekoia - Interlock ransomware evolving under the radar (IOCs extracted)
- Fortinet - Ransomware Roundup - Interlock
- SocPrime - Interlock Ransomware Detection: The FBI, CISA, and Partners Issue Joint Alert on Massive Attacks via the ClickFix Social Engineering Technique
- Forescout - A Year Later, Interlock Ransomware Keeps Leveling Up
- Talos Intelligence - Unwrapping the emerging Interlock ransomware attack
- GitHub - IOCs (Cisco-Talos Repo)
- GutHub - IOCs (ESentire Repo)
- ThreatFox - Interlock associated IOCs
- Centripetal - ClickFix and the New Era of Social Engineering
- Hunter Strategy - The Rise of Interlock Ransomware Group
Know what’s coming. Stop what’s next.
Sign up for our free threat alert bulletin service here.
The Cybercrime Barrier Your Organization Deserves
Sign up for a custom demonstration from our security team of how we bring together the best minds and most complete collection of threat intelligence to provide you with a shocking level of relief.