Critical Cisco Vulnerabilities Target the Network Edge
By Aileen Ward
Cisco has disclosed multiple critical vulnerabilities affecting core network management infrastructure including CVE-2026-20127 and CVE-2026-20079. CVE-2026-20127 impacts Cisco Catalyst SD-WAN (formerly Viptela) enabling attackers to bypass authentication mechanisms within the SD-WAN control plane. While CVE-2026-20079 affects Cisco Secure Firewall Management Center (FMC) and allows authentication bypass that can lead to full system compromise.
Both vulnerabilities target systems responsible for network orchestration and security policy management, meaning successful exploitation could provide attackers with broad visibility and control across enterprise environments. The targeting of these platforms reflects a broader trend: edge and control-plane infrastructure continues to be a high-value entry point for advanced threat actors, particularly when authentication controls can be bypassed remotely.
Overview CVE-2026-20127
A series of critical vulnerabilities had been disclosed affecting the Cisco Catalyst SD-WAN ecosystem. These vulnerabilities facilitate unauthenticated, remote attack chains that bypass peering authentication mechanisms can gain administrative control over the SD-WAN fabric. Five eyes intelligence agencies have issued advisories indicating nation-state actors and the threat actor UAT-8616 have been exploiting the flaw since 2023 to establishing footholds within government and corporate environments.
Vulnerability Type (CWE)
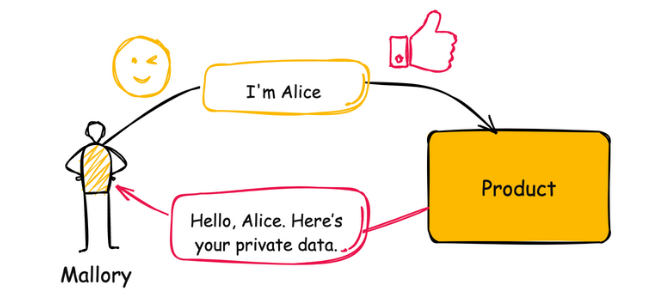
CWE-287: Improper Authentication CWE-287 occurs when an application incorrectly verifies the identity of a user, allowing attackers to bypass authentication or assume the privileges of other accounts.
CVSS Score
- Base Score: 10
- Attack Vector: Network (N)
- Attack Complexity: Low (L)
- Privileges Required: None (N)
- User Interaction: None (N)
- Scope: Changed (C)
- Confidentiality: High (H)
- Integrity: High (H)
- Availability: High (H)
Mitigation Steps
There are no workarounds that address this vulnerability. (Cisco, 2026) To ensure complete protection against these vulnerabilities and prevent future exploitation, Cisco emphasizes that customers must transition to the specific fixed software releases as outlined below.
| Current Affected Version | Status | Recommended Fixed Release |
|---|---|---|
| Prior to 20.9 | End of Maintenance | Migrate to a supported fixed release (e.g., 20.9.8.2+) |
| 20.9 | Supported | 20.9.8.2 |
| 20.11 | End of Maintenance | Migrate to 20.12.6.1 |
| 20.12.5 | Supported | 20.12.5.3 |
| 20.12.6 | Supported | 20.12.6.1 |
| 20.13 | End of Maintenance | Migrate to 20.15.4.2 |
| 20.14 | End of Maintenance | Migrate to 20.15.4.2 |
| 20.15 | Supported | 20.15.4.2 |
| 20.16 | End of Maintenance | Migrate to 20.18.2.1 |
| 20.18 | Supported | 20.18.2.1 |
Affected deployment types include:
- On-Premises
- Cisco Managed (Cloud)
- Cisco FedRAMP (Cloud)
- Cisco SD-WAN Cloud
Attack Chain
UAT-8616 uses a multi-stage attack chain designed for maximum stealth:
- Reconnaissance Identify internet-exposed Catalyst SD-WAN Manager or Controller interfaces.
- Initial Access (CVE-2026-20127) Exploit the peering authentication flaw via crafted requests to obtain a high-privileged, non-root user account.
- Privilege Escalation (Version Downgrade) Downgrade software to a version vulnerable to CVE-2022-20775 (a local privilege escalation flaw) to gain root access.
- Persistence Install persistent backdoors after achieving root access, then restore the original software version to hide evidence of the downgrade.
- Fabric Expansion Deploy rogue peers to maintain a permanent, encrypted presence in the network fabric.
Detection Strategy
Detection is challenging because actors frequently clean logs. Prioritize the following:
- Audit Control Connections Run
show control connectionsand investigate any System IP or Serial Number that doesn't match your inventory. - Log Anomalies Search
/var/log/auth.logfor successful logins from unexpected external IPs, specifically those linked tovmanage-adminor other high-privileged roles. - Unexpected Reboots Analyze
/var/volatile/log/vdebugfor evidence of unplanned reboots or software synchronization scripts (sw_script_synccdb.log) that indicate a version swap. - IPS Signatures Monitor for Snort/IPS triggers “
SERVER-OTHER TRUFFLEHUNTER SFVRT-1058 attack attempt“
Hardening Guidance from Cisco
Phase 1: Assess for Intrusion
Should exploitation have taken place, it is strongly advised that prior to applying patches, perform forensic preservation to ensure evidence of this exploitation is not deleted.
- Forensic Collection Capture snapshots of SD-WAN Manager/Controller instances and export all logs (/var/log/vsyslog, auth.log, and /var/log/nms).
- Compromise Assessment Audit show control connections for unrecognized Serial Numbers and review the Statistics Database for unexpected configuration changes.
- Patch Deployment Update to a fixed release (as refenced above). Patching the Manager and Controller remediates the core authentication bypass (CVE-2026-20127).
Phase 2: Network Perimeter & Access Control
Restrict the reachability of the management and control planes to authorized entities only.
| Category | Mitigation Action |
|---|---|
| Management Isolation | Move VPN 512 (Management) to a strictly Out-of-Band (OOB) network. Never expose ports 443, 22, or 830 to the internet. |
| Control Plane Security | Use ACLs to restrict UDP 12346 (DTLS) and TCP 23456 (TLS) to known Edge IP ranges. |
| Jump Hosts | Enforce access to SD-WAN Manager only through a hardened Jump Host protected by MFA (e.g., Duo). |
| Cisco-Hosted Rules | Use the SD-WAN Portal to define specific Inbound Rules; avoid "ALL" source IP rules. |
Phase 3: Identity and Authentication Hardening
Transition away from weak local credentials to centralized, multi-factor identity management.
- Implement RBAC Move away from the netadmin role for daily tasks. Assign operator, network_operations, or security_operations based on the principle of least privilege.
- Enforce MFA/SSO Integrate SD-WAN Manager with an Identity Provider (SAML/Okta/Azure AD) or enable native Duo MFA.
- Password Policy Configure "High Security" password criteria (15–32 characters, 8-character change delta). Update default configuration database credentials.
- SSH Security Use RSA Keys (2048-4096 bit) instead of passwords. Disable weak algorithms (SHA-1, AES-128) via SD-WAN Manager templates.
Phase 4: Data Plane & Logging Integrity
Ensure the fabric remains resilient and activity is auditable.
- Encrypted Fabric Maintain AES-GCM-256 for overlay tunnels. Use IPsec Pairwise Keys with ECDH P-384 for superior key exchange security.
- Session Management Set the Server Session Timeout to the minimum viable duration (default 30 mins) and configure CLI idle-timeout (e.g., 10 minutes).
- Centralized Logging Forward all logs to a remote Syslog/SIEM using TLS transport.
- Audit Retention Use the SD-WAN Manager API to estimate storage needs and expand the Audit Logs buffer (add a 20% buffer for growth) to meet compliance requirements.
Phase 5: Maintenance and Verification
- Web Certificates Replace default self-signed UI certificates with those signed by an Enterprise or Public CA.
- SNMPv3 Disable SNMPv1/v2; enforce SNMPv3 with authentication and privacy (AES/SHA).
- Regular Audits Periodically rotate SSH keys and administrative passwords, especially after an incident or staff offboarding.
Overview CVE-2026-20079
CVSS Score
- Base Score: 10
- Attack Vector: Network (N)
- Attack Complexity: Low (L)
- Privileges Required: None (N)
- User Interaction: None (N)
- Scope: Changed (C)
- Confidentiality: High (H)
- Integrity: High (H)
- Availability: High (H)
As of March 4th , Cisco has issued an additional critical security advisory referring to a severe authentication bypass vulnerability in their Secure Firewall Management Center (FMC) Software. CVE-2026-20079 has a CVSS Score of 10 (Critical) and could allow for a threat actor to bypass authentication, leading to full root access to the underlying operating system. This vulnerability originates from an improper system process activated at device boot. An attacker can exploit this vulnerability by sending crafted HTTP requests to a vulnerable device, allowing them to execute scripts and commands, gain privileged access and alter configurations. There are no advised workarounds issued for this CVE, immediate patching of affected devices is required. If unsure of whether a utilised Cisco product is affected by this vulnerability, Cisco customers are recommended to use the Cisco Software Checker tool to measure exposure.
Centripetal’s Perspective
Centripetal’s Velaris team continue to track and defend against threats like CVE-2026-20127 and CVE-2026-20079 for our customers. Consolidated threat intelligence deployed to protect our customers from the continued targeting and exploitation of edge devices, ensure that the intelligence gap is closed tighter.
High-severity zero-days and edge device exploitation are not new techniques, they continue to represent high-value initial access vectors for many threat actors. This CVE underscores the necessity of a defense-in-depth security strategy to ensure environments are secure, particularly those at the perimeter that have significant control and potential detrimental impact should they be compromised.
UPDATE:
Since the drafting of this publication Cisco has warned of 2 further vulnerabilities under active exploitation affecting Catalyst SD-WAN Manager. (Cisco, 2026)
CVE-2026-20122 represents a high-severity arbitrary file overwrite risk, carrying a CVSS score of 7.1. This flaw allows a remote attacker who has already secured read-only credentials to exceed their intended permissions via API access. By exploiting this vulnerability, the attacker can replace or corrupt critical files on the local file system, potentially leading to system instability or unauthorized configuration changes.
CVE-2026-20128 is an information disclosure vulnerability with a CVSS score of 5.5 that facilitates lateral movement. In this scenario, an authenticated local attacker with standard vManage credentials can exploit the system to escalate their permissions. Successful exploitation allows the attacker to gain Data Collection Agent (DCA) user privileges, granting them access to data and system functions that should otherwise be restricted to higher-level service accounts.
| Affected Version Path | Recommended Fixed Release |
|---|---|
| Earlier than 20.91 | Migrate to a fixed release (see below) |
| Version 20.9 | 20.9.8.2 |
| Version 20.11 | 20.12.6.1 |
| Version 20.12 | 20.12.5.3 or 20.12.6.1 |
| Version 20.13 | 20.15.4.2 |
| Version 20.14 | 20.15.4.2 |
| Version 20.15 | 20.15.4.2 |
| Version 20.16 | 20.18.2.1 |
| Version 20.18 | 20.18.2.1 |
Resources
- https://nvd.nist.gov/vuln/detail/CVE-2026-20127
- https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-sdwan-rpa-EHchtZk
- https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-onprem-fmc-authbypass-5JPp45V2
- CVE-2026-20079 | Tenable®
- https://sec.cloudapps.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-sdwan-authbp-qwCX8D4v#:~:text=Exploitation and Public Announcements
- https://thehackernews.com/2026/03/cisco-confirms-active-exploitation-of.html
Know what’s coming. Stop what’s next.
Sign up for our free threat alert bulletin service here.
The Cybercrime Barrier Your Organization Deserves
Sign up for a custom demonstration from our security team of how we bring together the best minds and most complete collection of threat intelligence to provide you with a shocking level of relief.