Coruna iOS Exploit Kit: Observed Traffic Across Education and Government Sectors
By Aileen Ward
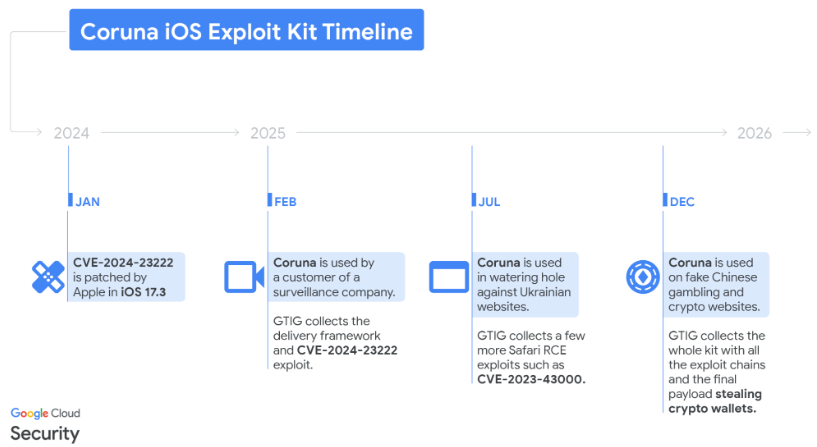
Coruna, an iOS exploitation framework containing full exploit chains and 23 individual exploits targeting iPhone models running iOS 13.0 through iOS 17.2.1, has been identified. The same kit is also under the name CryptoWaters.
Coruna's proliferation has been tracked across three distinct threat actors: a commercial surveillance vendor customer, UNC6353, a suspected Russian espionage group that conducted watering hole attacks against Ukrainian users, and UNC6691, a financially motivated threat actor operating from China (Google, 2026).
iVerify describes this as the first observed mass exploitation of iOS devices by a criminal group using nation-state-grade tools (iVerify, 2026). The codebase contains extensive inline documentation and comments written in native-level English (Google, 2026). Both Google and iVerify have noted that some of the exploits reuse vulnerabilities from the 2023 Operation Triangulation campaign discovered by Kaspersky. The definitive origin of the Coruna framework has not been established by any reporting party.
On March 7, 2026, two days after Google's publication, CISA added CVE-2023-41974 to their Known Exploited Vulnerabilities catalogue with a remediation deadline of March 26, 2026. This kernel use-after-free vulnerability (CVSS 3.1: 7.8 HIGH) represents the kernel privilege escalation component of the Coruna chain, and the NVD entry directly references Google's Coruna blog post as an exploit source (NadSec, 2026).
Campaign Details
UNC6691 deployed the Coruna exploit kit across a large set of fake Chinese websites predominantly themed around finance and cryptocurrency. The final payload, tracked as PLASMAGRID and using the identifier com.apple.assistd, is a stager that injects itself into the iOS powerd daemon running as root (Google, 2026).
iVerify's independent technical analysis reveals a multi-stage post-exploitation architecture. The initial implant running in powerd acts as a second stage, checking in with a command and control server to retrieve a configuration file and load a third stage component referred to internally as CorePayload. CorePayload executes within the locationd process and orchestrates all subsequent activity, including downloading and injecting additional modules into running processes. The imagent process is injected with a module that takes over C2 communication and includes a backup channel over SMS and iMessage. A separate module is injected into SpringBoard, which communicates with the locationd implant rather than directly with C2 infrastructure. None of the injected modules are code signed (iVerify, 2026).
PLASMAGRID's capabilities are financially motivated. The payload can decode QR codes from images stored on disk, analyze text blobs for BIP39 seed phrases and keywords such as "backup phrase" or "bank account," and exfiltrate matching content from Apple Memos to attacker-controlled C2 infrastructure. The locationd implant also directly inspects photos and Apple Notes on the device and uploads them. The malware additionally harvests photographs and emails beyond cryptocurrency wallet data (Google, 2026; iVerify, 2026).
The payload retrieves a remote configuration from its C2 to load additional modules targeting installed applications. Google identified 18 such modules targeting cryptocurrency wallet applications including MetaMask, Trust Wallet, Phantom, Uniswap, and TonKeeper (Google, 2026). iVerify's independent analysis recovered additional modules targeting WhatsApp and OKEx, indicating the kit is in active development and expanding its target set beyond the applications documented in Google's initial reporting (iVerify, 2026).
The exploit code features extensive documentation authored in native English, whilst the PLASMAGRID modules contain logging strings written in Chinese and some comments that may be LLM generated. This linguistic separation suggests the original exploit developers are distinct from UNC6691 (Google, 2026). PLASMAGRID communicates over HTTPS, encrypting collected data with AES. The implant contains hardcoded C2 domains and a fallback domain generation algorithm seeded with the string "lazarus" that produces 15 character domains under the .xyz TLD.
The malware lacks persistence and resides primarily in RAM. Restarting an infected device clears the infection, though the device can be reinfected if the user revisits a malicious site. NadSec's analysis of the JavaScript source confirms that the entire chain from watering hole landing to data exfiltration executes within the browser process without dropping any files to disk (NadSec, 2026). Affected users should reset passwords for any online services accessed from their device and enable two factor authentication on all critical accounts (iVerify, 2026).
Delivery & Attack Chain
When a user visits a UNC6691-controlled or compromised website from an iOS device, a hidden iFrame is injected that delivers the exploit kit. The framework fingerprints the device to determine the iPhone model and iOS version, then selects the appropriate WebKit remote code execution exploit followed by a pointer authentication code bypass. Post RCE, a binary loader delivers the next stage exploit chain payloads (Google, 2026). The chain has been characterised as a one-click exploit consisting of remote code execution in Safari and a local privilege escalation that allows attackers to take full control over infected devices. No user interaction is required beyond visiting the page (iVerify, 2026).
The exploit chains did not contain any specific targeting or one-time links. Any user visiting a delivery site with a vulnerable iOS version could be infected, and iVerify confirmed the ability to reinfect devices multiple times (iVerify, 2026).
The exploit chains leverage a mix of publicly known CVEs and non-public exploitation techniques. Key vulnerabilities within the kit include CVE-2024-23222, a WebKit type confusion vulnerability used for initial RCE on iOS 16.6 through 17.2.1; CVE-2022-48503, used for WebKit memory access on iOS 15.2 through 15.5; and CVE-2023-32409 and CVE-2023-32434, which provide sandbox escape and kernel privilege escalation respectively. CVE-2023-32434 and CVE-2023-38606 were also exploited as zero days in Operation Triangulation, discovered by Kaspersky in 2023 (Google, 2026). CVE-2023-41974, a kernel use-after-free added to the CISA KEV on 7 March 2026, provides the kernel privilege escalation that follows the WebKit RCE and PAC bypass stages (NadSec, 2026). The kit additionally includes advanced techniques to bypass Apple's Pointer Authentication Code and Page Protection Layer mitigations across multiple iOS versions.
| CVE Identifier | Vulnerability Type | Targeted iOS Versions | Role in Attack Chain |
|---|---|---|---|
| CVE-2024-23222 | WebKit Type Confusion | 16.6 through 17.2.1 | Initial RCE: Executes malicious code via the browser. |
| CVE-2022-48503 | WebKit Out-of-Bounds Memory Access | 15.2 through 15.5 | Information Leak: Aids in bypassing memory protections. |
| CVE-2023-32409 | WebKit Sandbox Escape | Various | Sandbox Escape: Allows the exploit to break out of the browser's restricted environment. |
| CVE-2023-32434 | Kernel Integer Overflow | Various | Privilege Escalation: Grants the attacker root/kernel-level access. |
| CVE-2023-38606 | Kernel Hardware Register State | Various | Mitigation Bypass: Used to circumvent Apple’s Page Protection Layer (PPL). |
| CVE-2023-41974 | Kernel Use-After-Free (CWE-416) | Pre-iOS 17 | Kernel Privilege Escalation: Added to CISA KEV on 7 March 2026 (CVSS 3.1: 7.8 HIGH). |
NadSec's reverse engineering of the JavaScript source provides additional detail on the post-RCE exploitation mechanics that Google described as "non-public exploitation techniques." The kit contains three independent WebKit RCE paths selected at runtime based on platform and Safari version: a NaN-boxing type confusion for macOS, a JIT structure check elimination with a Web Worker retry mechanism as a macOS fallback, and an OfflineAudioContext heap corruption chain combined with SVG attribute manipulation for iOS. All three converge on a common arbitrary memory read/write primitive (NadSec, 2026).
From that primitive, the chain progresses through four escalation stages. A 306-byte WebAssembly module constructed inline in JavaScript is compiled and its dispatch pointer hijacked to convert the Wasm sandbox into a native function call primitive. This enables a PAC bypass implemented as a confused deputy attack; rather than forging PAC signatures, the exploit temporarily swaps unsigned Global Offset Table entries in Apple's own system frameworks, then triggers legitimate PAC-authenticated call paths that read the attacker-substituted data. The original values are restored immediately after execution. The exploit then allocates read-write-execute memory via mach_vm_allocate from inside the WebContent sandbox, and finally bypasses Apple's JIT cage code integrity verification by reimplementing the PACDB rolling hash algorithm in JavaScript, using the hardware's own per-process PAC keys to produce valid signatures for arbitrary shellcode. The kernel cannot distinguish these forged hashes from legitimate JIT compilations (NadSec, 2026).
The delivery framework performs multiple validation checks. The initial RCE stage verifies the device is running iOS in Safari, checks for the presence of Lockdown Mode, and terminates if detected. The local privilege escalation stage checks for the presence of a Corellium virtualized iOS environment and removes crashlogs from previous exploitation attempts involving WebContent, powerd, and kernel panics, cleaning up evidence of unsuccessful prior infections (Google, 2026; iVerify, 2026). Additional technical characteristics of the delivery framework include the following: resources are referenced by hash values derived from a unique hardcoded cookie. Binary payloads are served from URLs ending in .min.js, encrypted with ChaCha20, packaged with a custom header of 0xf00dbeef, and compressed with LZW (Google, 2026). NadSec's analysis confirmed the JavaScript modules are organized as a custom module system with SHA-1 hash identifiers and dependency resolution, and that the kit contains version-adaptive offset tables covering 41 JSC internal structure offsets across three WebKit version thresholds, indicating systematic access to multiple WebKit builds during development (NadSec, 2026).
UNC6691's use of fake cryptocurrency exchange sites serves a dual purpose. Visiting a crypto exchange indicates the visitor's potential ownership of cryptocurrency wallets, whilst visiting from an iOS device triggers immediate delivery of the exploit kit. iVerify independently identified the domain mxbc-v2[.]tjbjdod[.]cn hosting exploits, along with C2 infrastructure at aidm8it5hf1jmtj[.]xyz and uawwydy3qas6ykv[.]xyz (iVerify, 2026). NadSec's analysis additionally documents b27[.]icu as a watering hole domain serving the Safari exploit chain (NadSec, 2026).
Operation Model
UNC6691 is a financially motivated threat actor operating from China. Unlike the earlier, highly targeted use of Coruna by UNC6353 against specific Ukrainian users, UNC6691 operates with a broader and less selective scope. The actor deployed the Coruna exploit kit across fake websites impersonating cryptocurrency exchanges, financial platforms, gambling sites, and pornography sites (Google, 2026; iVerify, 2026). This breadth of lure categories indicates UNC6691's intent to maximize the volume of compromised devices rather than pursue specific individuals.
The broader proliferation pattern is notable; the Coruna exploit kit moved from a commercial surveillance vendor's customer to a suspected Russian espionage group, UNC6353, and then to UNC6691. How this proliferation occurred is unclear but suggests an active market for secondhand zero day exploits (Google, 2026). The exploit market's role in proliferation has recent precedent. Australian national Peter Williams, a former executive at L3Harris subsidiary Trenchant, was sentenced to 87 months on 25 February 2026 for stealing at least eight of the company's exploits and selling them to a Russian broker believed to be associated with Operation Zero, which was subsequently sanctioned by the US Treasury Department the same week (Nextgov/FCW, 2026; NadSec, 2026).
The spyware market operates with minimal regulatory oversight, and once an exploit capability is sold, the original developer has no control over how it is subsequently used or redistributed. This dynamic mirrors the 2017 EternalBlue incident, where an NSA-developed Windows exploit was stolen and subsequently weaponized in the WannaCry and NotPetya attacks. Coruna follows the same pattern, now playing out on mobile devices (iVerify, 2026).
The Coruna exploit kit is not effective against the latest version of iOS. A portion of the exploit chain was patched with iOS 17.3. Updating to the most current iOS version is the primary mitigation, with Lockdown Mode recommended where an update is not possible (Google, 2026).
Centripetal’s Perspective
The traffic observed across international academic and government entities indicates that devices or users within these environments attempted to reach infrastructure directly tied to UNC6691's Coruna campaign and PLASMAGRID C2 operations. The majority of this traffic was shielded, which prevented the exploit delivery and C2 communication from completing. The domain 8fn4957c5g986jp[.]xyz, observed in the traffic, is consistent with this campaign’s DGA pattern. iphonex[.]mjdqw[.]cn communications serve as an exploit kit delivery endpoint for UNC6691. Given that the malware exfiltrates photographs, emails, and Apple Notes content in addition to cryptocurrency wallet data, the potential impact of a successful compromise extends beyond financial theft.
Organizations with traffic to this domain should review endpoint logs and confirm iOS patch levels on any devices that may have accessed it. iVerify's technical analysis provides specific forensic indicators that can assist in determining compromise, including the presence of the file com.apple.photolibraryd.plist in the device's preferences directory, evidence of the infection URL in Safari browser history, and anomalous network activity from the powerd and imagent processes in data usage logs. These artifacts can be observed across device restarts and are accessible through encrypted iTunes backups (iVerify, 2026).
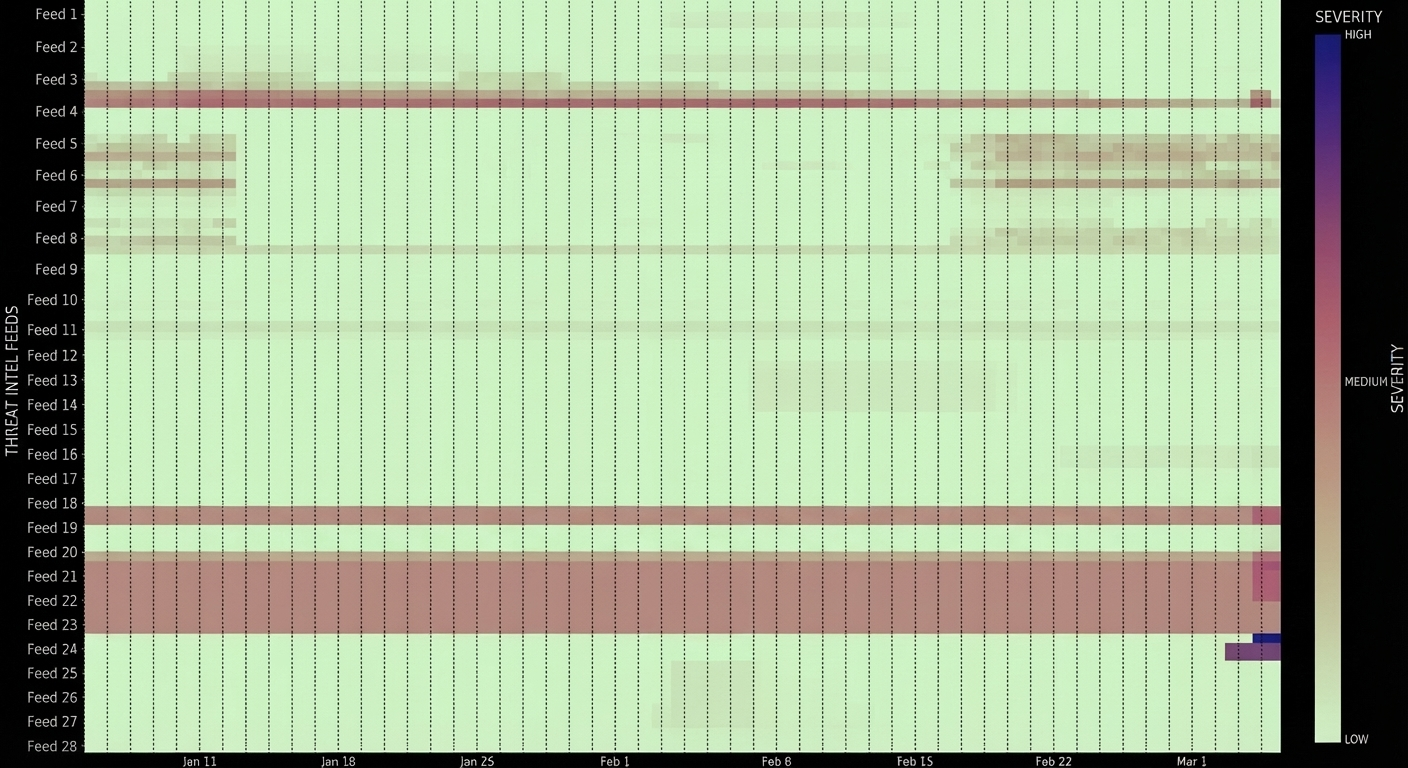
The concentration of this activity across education and government verticals is consistent with the broad, non-targeted delivery model described for this phase of the campaign, where any iOS device visiting the attacker-controlled sites would receive the exploit kit regardless of geolocation. This has been characterized as the first observed mass exploitation of iOS devices by a criminal group, marking a shift from the highly targeted deployment model historically associated with nation-state-grade exploit kits (iVerify, 2026).
The Coruna exploit kit represents a convergence of several concerning trends in the threat landscape: the proliferation of nation-state-grade capabilities to financially motivated actors, the commodification of iOS zero day chains through an under-regulated exploit brokerage market, and the resulting shift from targeted espionage deployment to indiscriminate mass exploitation. The traffic observed in Centripetal's customer environments across education and government sectors confirms that this campaign's reach extends to organizational verticals where device management and iOS patching may not be uniformly enforced.
The technical sophistication of the Coruna framework is substantial. The kit's five exploit chains cover nearly every iPhone model released over a four year period, and NadSec's independent reverse engineering of the JavaScript source reveals engineering quality consistent with professional development: version-adaptive offset tables, retry mechanisms, fallback exploit paths, and a PAC bypass technique that exploits a design level gap between control flow and data flow protections that software updates alone cannot fully address. The addition of CVE-2023-41974 to the CISA KEV catalogue on March 7, 2026, with its March 26th remediation deadline, reinforces the urgency of patching and establishes a federal compliance requirement for affected organizations.
The proliferation path from commercial surveillance vendor to Russian espionage group to Chinese criminal actor illustrates the lifecycle risk inherent in offensive exploit development. The sentencing of Peter Williams for selling stolen exploits to a sanctioned Russian broker provides a concrete link between exploit theft and the downstream harms observed in this campaign. Once a capability of this calibre enters the secondary market, the original developer's control over targeting, scope, and restraint is permanently lost.
For organizations with traffic to the identified infrastructure, the immediate priorities are confirming iOS patch levels across all managed devices, reviewing endpoint and network logs for the forensic indicators detailed in this report, and restarting any potentially affected devices as an interim remediation measure. The PLASMAGRID DGA pattern and the expanding set of delivery domains, now including b27[.]icu alongside the previously documented UNC6691 infrastructure, should be incorporated into network monitoring and blocking rules. Both Google and iVerify have indicated that further technical analysis will be published, and this finding should be revisited as additional details emerge.
IOCs
| Indicator | Type | Context |
|---|---|---|
| mxbc-v2[.]tjbjdod[.]cn | Domain | Exploit kit delivery endpoint operated by UNC6691 (iVerify) |
| iphonex[.]mjdqw[.]cn | Domain | Exploit kit delivery endpoint for UNC6691 (Centripetal) |
| b27[.]icu | Domain | Watering hole domain serving Safari exploit chain (NadSec) |
| aidm8it5hf1jmtj[.]xyz | Domain | PLASMAGRID C2 infrastructure (iVerify) |
| uawwydy3qas6ykv[.]xyz | Domain | PLASMAGRID C2 infrastructure (iVerify) |
| 8fn4957c5g986jp[.]xyz | Domain | DGA-generated domain consistent with PLASMAGRID pattern (Centripetal) |
Resources
- https://iverify.io/press-releases/first-known-mass-ios-attack
- https://www.securityweek.com/nation-state-ios-exploit-kit-coruna-found-powering-global-attacks/
- https://mezha.ua/en/news/coruna-russian-hackers-309111/amp/
- https://cloud.google.com/blog/topics/threat-intelligence/coruna-powerful-ios-exploit-kit
- https://404-founders.com/blog/coruna-how-your-iphone-can-be-hacked-without-a-click-and-how-to-protect-yourself
- https://iverify.io/blog/coruna-inside-the-nation-state-grade-ios-exploit-kit-we-ve-been-tracking
- https://www.nadsec.online/blog/coruna#article
Know what’s coming. Stop what’s next.
Sign up for our free threat alert bulletin service here.
The Cybercrime Barrier Your Organization Deserves
Sign up for a custom demonstration from our security team of how we bring together the best minds and most complete collection of threat intelligence to provide you with a shocking level of relief.